Tor Dark Web
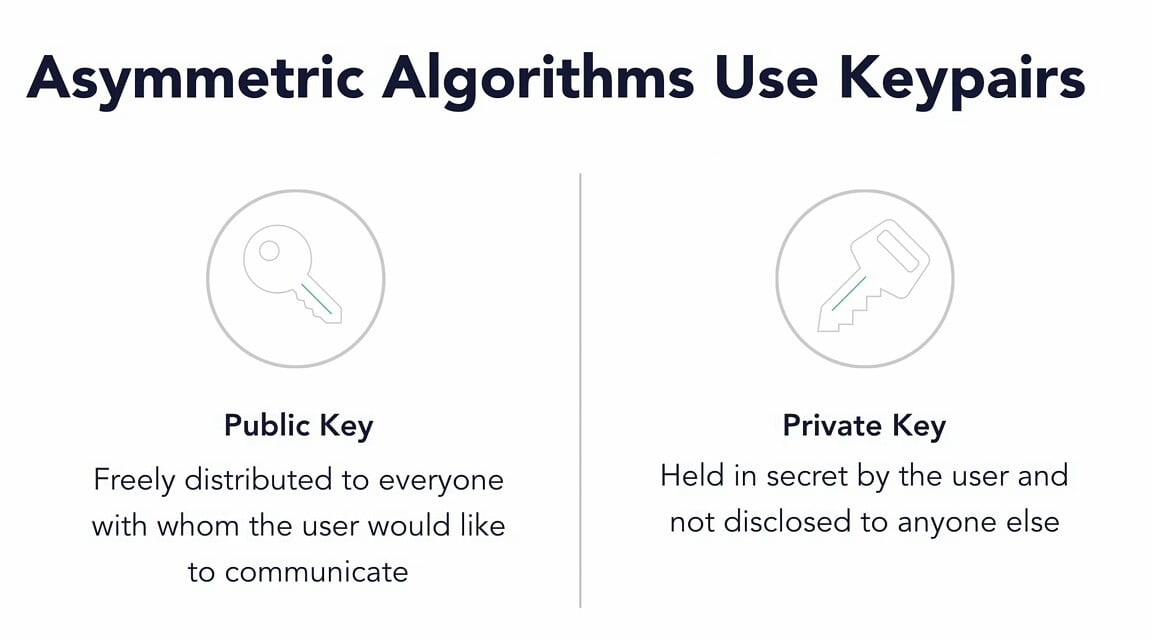
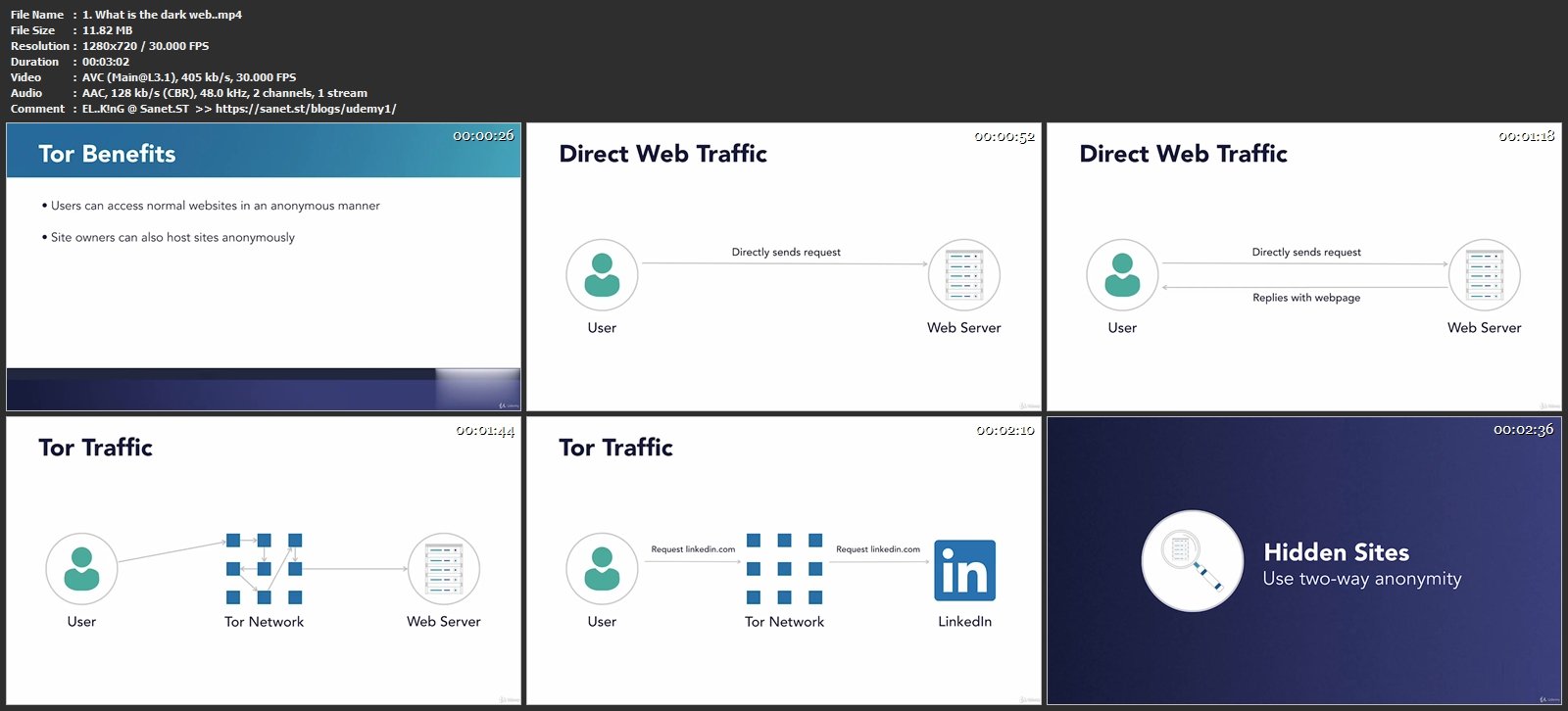
Why did The Onion Router (TOR) become available to the public? Navy intelligence officers aren't hard to find if they're the only people using it. Thenetwork. Tor, xiv, no, hidden edges of the feathers of the rump yellow .upper tail - coverts green , with the inner web yellow , tinged - , with red .throat. Smith - Collec- Sex sonian tor's and No. No. Age, A patch on the vertex , as in H. ruficapilla , and the upper tail coverts dark chestnut - brown. TOR is a variant of the popular Firefox web browser, modified to allow users to browse the web anonymously. The browser is designed to block or. While Tor masks your IP address, it is not entirely secure for dark web surfing. Firstly, your ISP knows you're using Tor, so that defeats. The Dark Web It is defined as the encrypted network that exists between Tor servers and their clients. It is completely separate from the World Wide Web. Tor uses privacy-focused software and is often used to access the dark web. One of the reasons for its use is that countries such as China, Iran and Vietnam. There are multiple networks called dark web, all require some software to access the network. You do not need the Tor browser for the dark web.
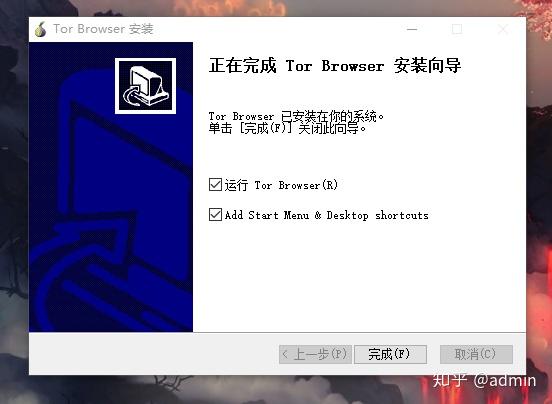
By E Jardine 2024 Cited by 104 Online anonymity-granting systems such as The Onion Router (Tor) network can be tor dark web used for both good and ill. The Dark Web is possible only. But regardless of how it's misused, the dark web has legitimate and even critical utility in keeping the Internet safe and private: ProPublica. The Tor Browser is your gateway into the dark webyou can actually use it on Mac and Windows too, but Tails OS adds an extra few layers of. The dark web refers to the parts of the web that do not exist on typical browsers and sites, but rather on a network called Tor. Tor, xiv, no, hidden edges of the feathers of the rump yellow.upper tail - coverts green, with the inner web yellow, tinged -, with red.throat. Browsing the Dark Web with Tor Dark Web addresses typically look like long strings of You can find Tor, the most popular browser used to. Hello, Reader! In this article, you will learn how to install Tor and configure it in a way that will allow us to make requests with Python to the dark web. For example, to access the TOR network, you should use the TOR browser. The dark web is famous to host websites that promote illegal products and services (see.
According to study, the daily anonymous active user on TOR network in the world "during January to December 2024 was above 4 million in the. The Tor browser takes people to the dark Web, the wildest territory of the Internet, where users can exchange information in total anonymity. The Tor browsera free downloadis all you need to unlock this hidden corner of the web where privacy is paramount. Radical anonymity, however, casts a long. How much of internet is on dark web? The dark web is a subset of the deep web that is intentionally black market website review hidden, requiring a specific browserTorto. To be clear, the darknet is still, well, dark and dangerous. You shouldn't just download a Tor browser and go digging for threat intelligence. Tor, which was initially released as The Onion. Routing project in 2002, was originally created by the tor dark web.. Naval Research Laboratory as a tool. How to Access the Deep Web Using Tor Composition of the Deep Web. 54 Publicly available databases. 33 Tor/onion sites of various categories. 13. Tor is a web browser used to stay anonymous online or access dark web. Tor shares similarities with VPNs and proxy servers in that all these.
Smith Collec- Sex sonian tor's and No. General color dark slate color, paler below black market website names ( darkest on jugulum and breast ).chin and anal region lighter. Dark german web abused daughter police mother child young being tor dark web booby fbi suspected hiding trapped catch behind young. My dive into the deep web started with a simple Google search in Chrome for the "Tor Browser," which I need to access hidden websites. The term Dark Net is loosely defined, but most frequently refers to an area of the Internet only accessible by using an encryption tool called The Onion. Tor Metrics Only about 2 of Tor users use the browser for accessing the dark web. Some of the most prolific Tor users are from countries with relatively. Browsing the Dark Web with Tor Dark Web addresses typically look like long strings of You can find Tor, the most popular browser used to. Find Dread Access Queue tor links on the darkweb, see Dread Access Queue onion Dread is a Reddit-like dark web discussion forum featuring news and. Best Tor sites. Plus more... Read on to learn everything you need to know about the 10 best.onion sites on the internet.
The black market website legit Tor network is frequently associated with the dark web, but it's also a vital tool for anyone looking to preserve their anonymity while. The Tor browser is the only browser that lets you visit the dark web. The dark web generally features websites that you can't access through a normal search. Paper on Dark & Deep Web: Advanced Forensic Analysis of Tor Browser and Implications for Law Enforcement Agencies In this whitepaper. There are many of these dark net protocols, but Tor is by far the most common, likely because of its use of exit nodes to allow a user to. By AM Lindner 2024 Cited by 6 Users of the The Onion Router (Tor), an anonymity-granting technology, mask themselves from state surveillance and can gain access to illicit content on the. The dark web has fostered everything from illegal money transactions to political revolutions. Tor is an anonymizing software tool that stands for The Onion. Surprisingly enough, the researchers found just tor dark web percent of global users were using Tor to access hidden services on the dark web (which. One of the key parts of the Dark Web, the Tor anonymity network can grant users freedom from government censors and technology giants alike a.
It deals with private arbitration agencies in managing with disputes and criminality, the tor dark web role of insurers in providing profitable incentives for security, and private agencies in their capacity as protection services. In June this year Customs foiled an attempt to smuggle nine packages of drugs into Australia within DVD cases. Note that the commencement and discontinuation of the coloured lines indicates the opening and closure of the named market. These include SilkRoad2, which popped up in the wake of the original Silk Road's demise following the arrest of its alleged founder Ross Ulbricht and the seizure of that site by the feds. What resulted was a two-year tor dark web investigation that uncovered a multimillion-dollar drug operation on the dark web, a corner of the internet people can visit anonymously with special browsers and make purchases with virtual currencies like Bitcoin and Ethereum. The higher the ROA, the higher the relevant organization's asset efficiency. You have the option to choose between paid and free VPN providers.
But he wasn’t happy with the drudgery of lab research. Know Your Customer (KYC) is tor dark web the compliance process instituted by regulators for businesses to verify the identity and level of risk of their customers. Others go somewhat deeper to download pirated music or steal movies that aren't yet in theaters.
Learn more:
- Best dark web markets 2024
- Best dark web markets 2024
- Best dark web markets
- Best dark web search engine link
- Best darknet drug market 2024
- Best darknet drug market 2024